
Wedge Cloud Network Defense™ (WedgeCND™), powered by the Wedge Absolute Real-time Protection (WedgeARP™) platform, is a cloud-managed, on-premises or cloud-enforced security service offering that provides a vast array of optimized Security-as-a-Service (SECaaS) features to enterprises. It enables effective security solutions for any Cloud-connected computing devices; providing scalability, flexibility and accuracy for enterprise customers.
Wedge Cloud Network Defense™ provides real-time threat protection for all types of endpoints in different types of networks (mobile data, 5G, SD-WAN, SASE, and smart-city/IIoT). It enables situation awareness for the entirety of managed networks, with security event tracing, rapid response, centralized policy management, reporting, and analytics. Based on the WedgeARP™ platform, it has the deepest visibility of network data in the industry, possessing an unmatched ability to defend against malicious attacks that are undetectable with shallow inspection techniques.
With an embedded deep learning AI engine, WedgeCND™ can detect never-before-seen malware in milliseconds. Running on an orchestrated threat management platform, it is a novel approach that provides real-time large scale security implementations with effective threat management services.
We have been perfecting information security safeguards for fifty years, yet organizations are more at risk than ever. Why? Because the definition of the “network” has fundamentally shifted. We’ve replaced the “everything inside the firewall” network model with an amorphous patchwork of public, private and carrier clouds.
Furthermore, endpoints now include smartphones, tablets and devices like cars, thermostats and even industrial equipment: Devices which now connect from anywhere in the world, mostly outside your firewall.
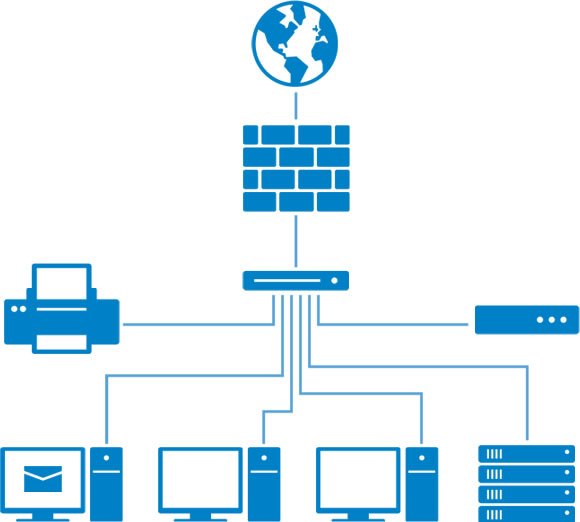
Traditional network security focused on hardening the edges of the network. Safeguards like firewalls and access solutions at the outer edge and anti-virus and anti-malware at the inner edge — the endpoint.
But what does “edge” even mean in a network comprised of multiple data centers, dozens of public and private clouds, three or four carrier networks and endpoints that include smartphones and tablets?
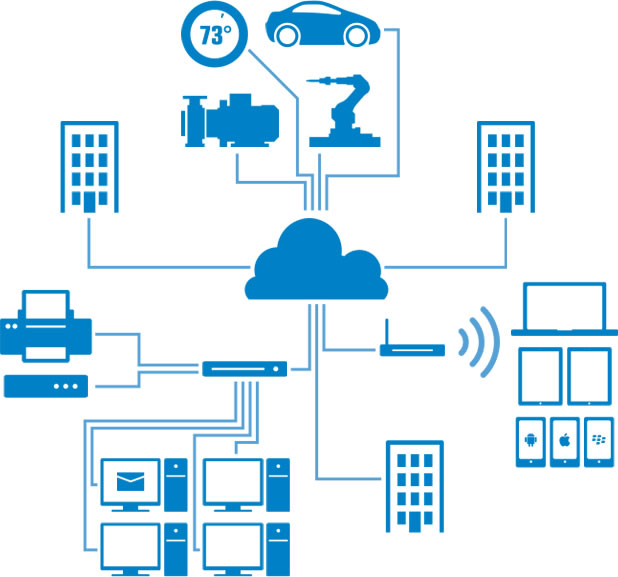
The cloud is now the center of your network. It is the last stop for traffic entering and the first stop for traffic leaving your organization. The cloud is where you need to implement the security that protects your valuable information and compute infrastructure.
In short, the cloud is your new edge.