WedgeAMB integrates multiple best-in-class virus and malware detection technologies that are orchestrated with WedgeSO. The first step in the process is WedgeAMB’s intrusion prevention system (IPS) level scanning to detect and block worms and other layer 3 threats. Next, the DCI engine separates content that should be scanned for malware from content that will not be scanned, such as VOIP traffic, streaming video, and other customer specified content.
All remaining traffic and associated content is then scanned using Wedge’s full library of more than 100 million known virus and malware signatures sourced from third party anti-malware partners. The same content is then scanned using Wedge’s Heuristics detection engine to detect and block new variants of known threats. Collectively, these scans reliably detect and block more than 99% of viruses and malware that may exist in typical enterprise networks today.
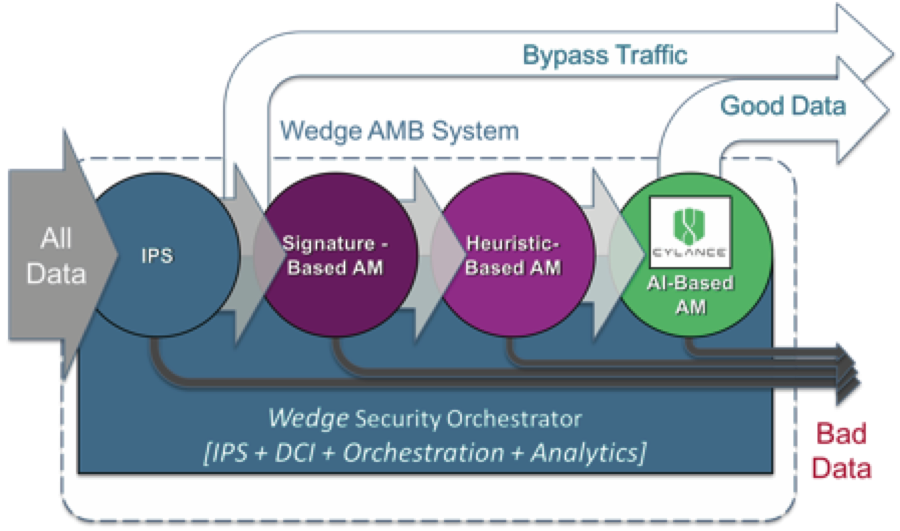
All remaining traffic is then further analyzed using Cylance® artificial intelligence (AI) predictive malware prevention engines to detect and block any remaining zero-days, targeted, and other advanced persistent threats that may be present. Cylance’s industry leading predictive malware prevention engine combines machine learning with artificial intelligence to yield the highest real-time threat detection accuracy available. Collectively, this multi-layered anti-malware approach leverages WedgeSO’s single inspection and content reconstruction cycle to provide the industry’s highest accuracy detection of both known and unknown threats, with only milliseconds of latency.
As an option, data identified as suspicious by not confirmed to be malware may be forwarded to WedgeMA for further evaluation.
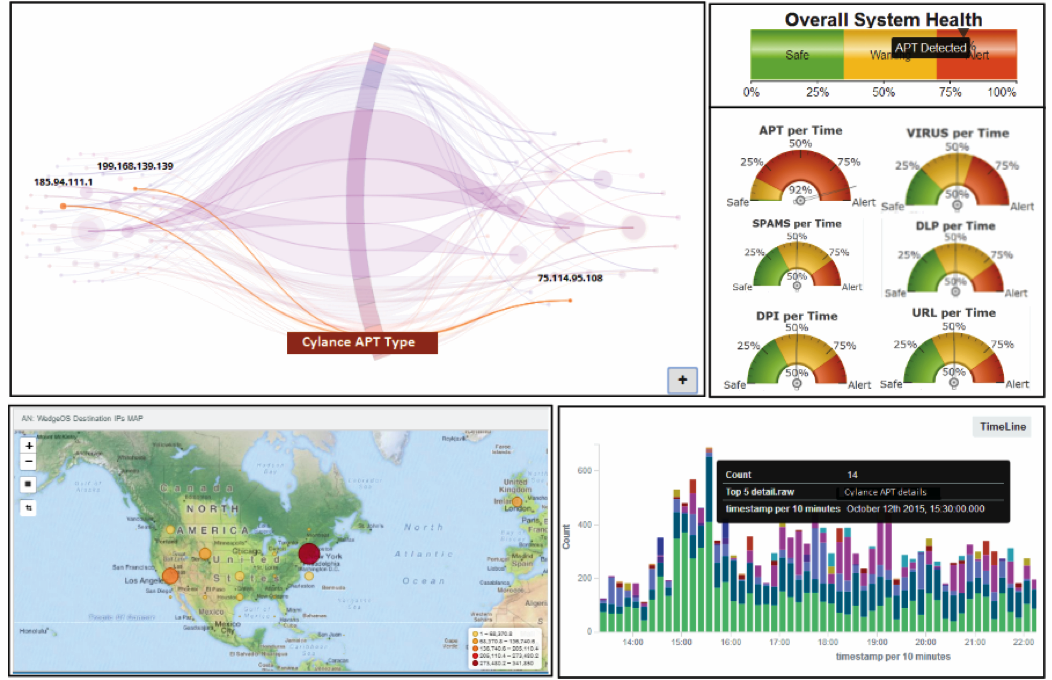
Network Wide Visibility and Threat Analytics
WedgeAMB integrates the WedgeIQ™ threat analytics and intelligence engine to provide network wide visibility into the types, quantity, origination, and targets of WedgeAMB blocked threats across the network. Threat intelligence is rolled up from each WedgeAMB system, for analysis and visualization using advanced graphing techniques to render complex data sets as intuitive and actionable information. Real-time visibility to the network-wide threat landscape empowers security professionals with the intelligence they need to identify and act on the most critical threats, further maximizing security.